Set up and authentication
How to get access to the POAP API
The POAP API has two types of endpoints:
- Open endpoints, which can be called with just an API key
- Authenticated endpoints, which require a valid access token to return a response.
Before requesting API keys, confirm whether the use case you have in mind will require access to the following endpoints:
Protected Endpoints
- POST /actions/claim-qr : Mint a POAP to a collector with an existing mint link.
- GET /actions/claim-qr : Get status and information about an individual mint link including the claim status, and information about the event it belongs to, as well as the collector and transaction (if applicable).
- POST /event/validate : Check if a secret code for a particular event is valid.
- POST /event/{id}/qr-codes : Returns the list of six digit mint codes for a particular event, along with the claim status of each code for whether it has been claimed yet.
- POST /redeem-requests : Request more mints for mint links, Websites, or Secrets.
- GET /secret/{secret_word} - Obtain information about a specific secret word claims and its related event.
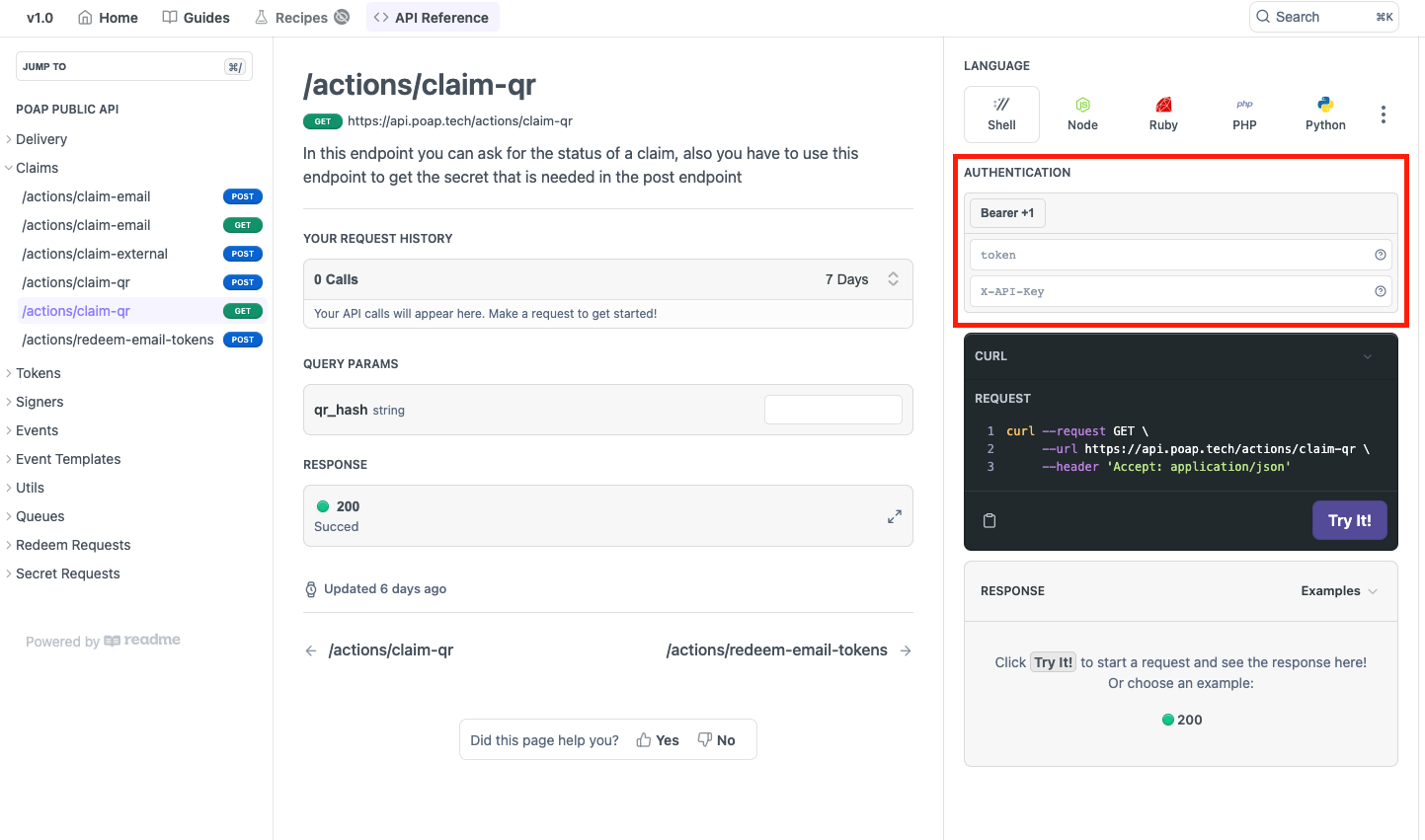
Check if the endpoints you would like to use have a token parameter in the Authentication section of the API Reference.
Calling the API
Authentication to the API is performed via HTTP basic authentication.
All requests should contain the header X-API-Key={apikey} where {apikey} is your unique API key.
For example, a header with the API key would look like this:
curl -vvv -H "X-API-Key: $apikey" https://api.poap.tech/events/id/16947Generating an access token
Once you have an API key, your Client ID and Client Secret, you can call the POAP API to generate an access token. This token will be valid for 24 hours, at which point your application will need to regenerate it.
After requesting an auth token and receiving your credentials, you can use the following command to generate an access token. You will need to populate audience, client_credentials, and client_secret (auth token) with the values provided via email:
curl --location --request POST \
--url 'https://auth.accounts.poap.xyz/oauth/token' \
--header "Content-Type: application/json" \
-d '{"audience": "https://api.poap.tech", "grant_type": "client_credentials", "client_id": "$clientid", "client_secret": "$clientsecret"}'Usage
API keys, authentication tokens, and access tokens should be stored securely in a Secrets Manager or environment variables at runtime, and never exposed in your application codebase.
You can call protected endpoints using your access token by inserting it into the header as follows:
curl --location --request GET \
--url https://api.poap.tech/actions/claim-qr?qr_hash=1kozmm' \
--header 'Accept: application/json' \
--header 'Authorization: Bearer $acccesstoken' \
--header 'X-API-Key: $apikey'For HTTP requests, make sure to include the following headers to authenticate your request:
GET /actions/claim-qr HTTP/1.1
Authorization: Bearer {accesstoken}
Accept: application/json
Host: api.poap.techGet API access
API keys and authentication tokens are available by completing this form.
Updated 7 months ago
